Blog ►
HissenIT Blog: Programming, Software Development, Java
You can follow this blog through this news feed or our social media channels.
Previous publications can be found in the publication archive.
Understanding CSV Files: What they are and how to use (How-to)
 Using CSV files is a daily routine for many people who have to accomplish a - fully automatic or semiautomatic - data exchange between different IT systems. CSV files are not the only solution path, but are very common. This concerns for instance online and e-commerce businesses which import the current orders from eBay into their own ERP system (Enterprise Resource Planning) or the accounting when exporting tax data to the tax office.
...
Using CSV files is a daily routine for many people who have to accomplish a - fully automatic or semiautomatic - data exchange between different IT systems. CSV files are not the only solution path, but are very common. This concerns for instance online and e-commerce businesses which import the current orders from eBay into their own ERP system (Enterprise Resource Planning) or the accounting when exporting tax data to the tax office.
...
Windows 11 Certificate-based File Encryption (CrococryptFile with Hardware/Software Token)
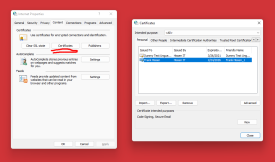 HissenIT's CrococryptFile fully supports Windows 11 including crypto suites. Besides classical end-user password-based encryption of files and folders, also the Windows Keystore using certificate tokens can be used. Hence, existing PKI infrastructure components can be used to encrypt file archives quickly also in business groups.
...
HissenIT's CrococryptFile fully supports Windows 11 including crypto suites. Besides classical end-user password-based encryption of files and folders, also the Windows Keystore using certificate tokens can be used. Hence, existing PKI infrastructure components can be used to encrypt file archives quickly also in business groups.
...
Secure Programming of Web Applications: Authentification
 We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
Secure Programming of Web Applications: Session-Hijacking
 We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
Secure Programming of Web Applications: Clickjacking
 We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
Secure Programming of Web Applications: Remote File Inclusion (RFI) and Local File Inclusion (LFI) resp. Directory/Path Traversal
 We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
Secure Programming of Web Applications: Open Redirection
 We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
Secure Programming of Web Applications: Cross-Site Scripting (XSS)
 We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
Secure Programming of Web Applications: Cross-Site Request Forgery (CSRF)
 We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
Secure Programming of Web Applications: SQL Code Injection
 We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
We can read about numerous successful attacks on well-known web applications on a weekly basis. Reason enough to study the background of "Web Application Security" of custom-made / self-developed applications - no matter if these are used only internally or with public access.
...
JavaFX WebView / WebKit error at JavaScript to Java communication (Java 8)
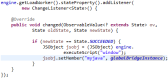 We are using Java for nearly two decades to build products. When an integrated WebKit was finally introduced to the Java platform - coming with JavaFX - development opportunities were boosted tremendously, because now you are able to integrate HTML5 web technologies into your desktop application easily.
...
We are using Java for nearly two decades to build products. When an integrated WebKit was finally introduced to the Java platform - coming with JavaFX - development opportunities were boosted tremendously, because now you are able to integrate HTML5 web technologies into your desktop application easily.
...
Say no to plain passwords: Secure Password Hashing
 Plaintext passwords should not be used anymore. You are probably using a web shop software framework that takes already care of this. Most application frameworks in the world do not use plain passwords anymore but password hashes instead.
...
Plaintext passwords should not be used anymore. You are probably using a web shop software framework that takes already care of this. Most application frameworks in the world do not use plain passwords anymore but password hashes instead.
...
Encryption background: What is key wrapping?
 Key wrapping is a simple technique in cryptography that is used in almost all common encryption technologies.
...
Key wrapping is a simple technique in cryptography that is used in almost all common encryption technologies.
...
Open-Source and Security: Why Open-Source is not insecure
 Recently, I received the question if it would not be dangerous, when the source code for an encryption software is publicly available. An answer...
...
Recently, I received the question if it would not be dangerous, when the source code for an encryption software is publicly available. An answer...
...
Password-based Encryption made easy
Easy encryption for Android apps – CrococryptLib 1.4 released
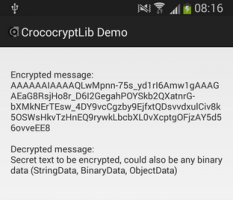 CrococryptLib 1.4 for Android released: A library for mobile apps that allows the most easiest integration of password-based encryption, hashes and other cryptography operations. No in-depth cryptography knowledge is required to integrate encryption into Android apps.
...
CrococryptLib 1.4 for Android released: A library for mobile apps that allows the most easiest integration of password-based encryption, hashes and other cryptography operations. No in-depth cryptography knowledge is required to integrate encryption into Android apps.
...
The easiest way to integrate encryption into enterprise applications – HissenIT released CrococryptLib
 HissenIT recently released CrococryptLib for Java: A library for Java back-end, desktop and mobile applications that allows the most easiest integration of encryption and other cryptography operations. No in-depth cryptography knowledge is required to integrate encryption into
enterprise applications or software products.
...
HissenIT recently released CrococryptLib for Java: A library for Java back-end, desktop and mobile applications that allows the most easiest integration of encryption and other cryptography operations. No in-depth cryptography knowledge is required to integrate encryption into
enterprise applications or software products.
...